Zero Standing Privilege.
Zero Technician Disruption.
Your technicians are sharing customer admin credentials.
There is no way to trace which technician took which action, no automatic password rotation when someone leaves, and one compromised credential exposes every client in your stack.
QGuard eliminates it.
Trusted by 1,200+ MSP partners to eliminate shared standing credentials—without disrupting the way technicians work.
















The Problem With Shared Admin Access
One shared credential.
Every client environment is exposed.
Most MSPs manage client access the same way: a shared admin account stored in IT Glue or Hudu, and every technician using the same credential. One phishing email, one departing technician, one compromised entry — and there is no way to know which clients were accessed, by whom, or what was done.
Shared credentials were never designed for accountability. They were designed for convenience.
Privilege is an event.
Not a state.
QGuard Just-in-Time access decouples the privilege from the technician's standing identity entirely. Access is provisioned only for the specific task required and automatically deprovisioned when the work is done.
No shared credential. No standing access. No attack surface between sessions.
From Discovery to Zero Standing Privilege
Most MSPs don't need a rip-and-replace implementation project. They need three things: visibility into what exists, control over who can access what, and access that disappears when the work is done. QGuard delivers all three — deployed through the tools you already use.
Find Every Shadow Credential
Set Technician Access Policies
Technicians Login — No Credentials Required
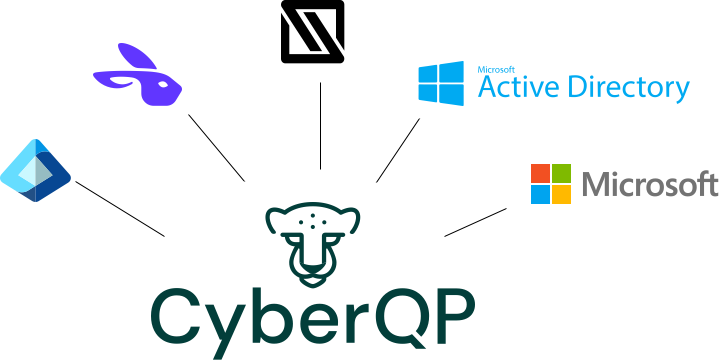
An orchestration layer. Not a replacement.
We integrate directly with IT Glue and Hudu, your whole Microsoft stack — Entra ID, Active Directory, and Local Windows Accounts — and deploy through your existing RMM. Your documentation system stays. Your RMM stays. Your identity stack stays. We add Just-in-Time access on top of the tools you already have. Nothing is ripped out. Nothing is rearchitected.
What MSPs say the moment they see it.
"It's night and day. I know who to fire when something breaks."
"Changing passwords when someone leaves often doesn't happen — it's impossible to change that many."
"They were facing a 45% insurance increase. After implementation they got a 15% decrease — a 60% turnaround."
How the Shared Credential Model stacks up against QGuard Just-in-Time Access.
Most MSPs have never used a PAM solution. This is a direct comparison between the shared credential model most MSPs rely on today and what QGuard makes possible.
This is what Zero Standing Privilege looks like in practice.
The technician you let go last quarter still knows the passwords to every client environment you manage.
Start your 30-day Proof of Concept. White-glove onboarding included.
In the meantime, if you want to see the JIT workflow before you dig in yourself, reply to any of our emails and we'll jump on a quick call.
